How to Avoid Phishing With Proxies?
Flipnode on Apr 24 2023
Phishing attacks continue to be a prominent method for harvesting credentials, distributing malware, and committing fraud. In fact, according to the 2020 Data Breach Investigations Report, phishing ranked as the second most common type of threat that penetrated organizations' security and the leading type of threat in data breaches.
Unfortunately, cybercriminals are constantly improving their tactics and carrying out well-planned, prolonged attacks by adapting and incorporating the latest trends.
Meanwhile, cybersecurity companies are taking a proactive approach by monitoring vast amounts of data on multiple targets in their ongoing battle against threat actors. This article will examine the primary types of modern phishing attacks and explore the challenges that cybersecurity professionals face. Additionally, we will outline advanced measures, such as using Datacenter Proxies, that bolster the fight against phishing campaigns.
Phishing attacks are on the rise
The objective of a phishing attack is to deceive the recipient into divulging confidential data such as login credentials, Social Security numbers, or other sensitive information. Scammers employ emails, phony websites, phone calls, or text messages to grab the victim's attention and prompt them to take the desired action. Additionally, they constantly invent novel methods to exploit and capitalize on the public's desire for trustworthy information.
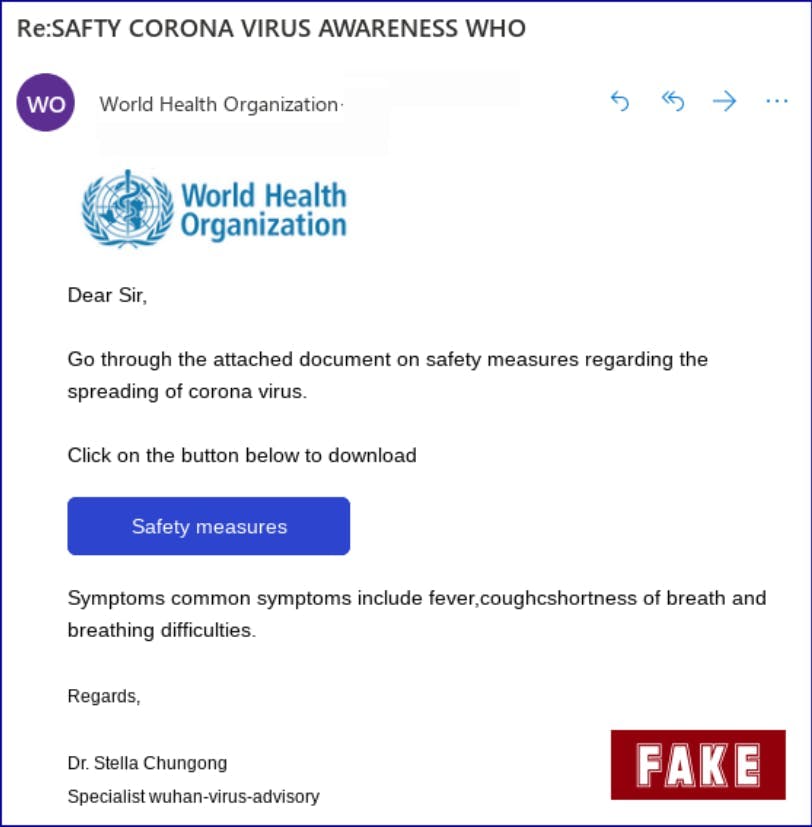
In a recent report by Google, it was revealed that the number of phishing websites soared from 149,195 in January 2020 to 522,495 in March, marking a 350% surge in two months. The report also highlighted that a majority of these websites were linked to the COVID-19 pandemic narrative, serving as a decoy.
At the peak of the global pandemic, cybercriminals exploited COVID-19 related terms and primarily targeted three main objectives, which are as follows:
- Encouraging individuals to donate to bogus charities
- Stealing login credentials
- Distributing malware
According to the Internet Organized Crime Threat Assessment 2020 by Europol, cybercriminals altered their storyline to fit the COVID-19 pandemic. Nevertheless, the review highlighted that the fundamentals of cybercrime remain mostly unchanged.
How phishing scams work: sophisticated methods
As phishing attacks become more advanced, organizations are finding it challenging to differentiate between genuine and fraudulent attempts and to recognize warning signs. Scammers continuously develop new tactics and adapt their methods to suit current events, making it more challenging to detect and prevent such threats.
Despite cybersecurity companies' efforts to monitor and expose phishing incidents, time is a crucial factor in addressing such threats. Scammers often use multi-faceted attack campaigns that are fleeting, making it difficult for organizations to defend against them. By tailoring their approach to the situation, scammers trick victims into providing sensitive information, enabling them to access systems undetected.
Various types of phishing attacks utilize different methods, but spear phishing and deceptive phishing are the most common ones. While the number of phishing attacks is on the rise, these two techniques remain the most prevalent.
Deceptive phishing
Deceptive phishing is the most commonly used method of phishing. Attackers often impersonate a legitimate company to obtain sensitive information. They use scare tactics to urge recipients to act quickly and give them the desired attention.
Fraudsters usually create phishing websites by combining legitimate and malicious code. They copy the CSS and JavaScript of a well-known organization's login page and make minor changes to the code. This makes the website appear genuine, and victims enter their login credentials unknowingly.
Another example of deceptive phishing involves modifying the logos of well-known brands and incorporating them into phishing emails or malicious websites. Attackers adjust an HTML attribute to evade email filters. Emails with these altered logos appear more authentic and may deceive recipients into thinking that the attack message is legitimate.
Spear phishing
Spear phishing attacks are targeted towards specific individuals rather than random groups, making them more personalized. Cybercriminals conduct research on their victims' personal information, such as name, company name, and job position, to create customized email or website forgeries. These attacks may seem more legitimate due to their well-orchestrated approach, which includes a malicious URL or malware attachment. Moreover, these attacks have a higher success rate, and most standard spam filters fail to detect them, making standard protection measures ineffective.
In addition to including specific context, attackers add another layer of effort when approaching their victims. Instead of relying on a single email, they perform multi-stage attacks that may involve other forms of communication, such as a phone call from a fake customer support agent. To create a false sense of security, scammers may even imitate the specific accent or refer to recent local events.
Spear phishing attacks are common on social media platforms such as LinkedIn. Cybercriminals can infiltrate via fake accounts, make connections, and learn about the company's structure to plan future attacks and create personalized emails.
Improving security with proactive capabilities
As phishing attackers continue to evolve, cybersecurity companies are taking proactive measures to combat cybercrime. Due to the rapid pace of phishing attacks, it's vital to gather data efficiently and quickly in order to scan the web or internal systems for existing and potential threats and gain full visibility.
Most phishing campaigns aren't new but rather updated and customized to sync with current events and attract attention. This means that organizations need to implement prompt monitoring and make data-driven decisions.
In addition to reactive measures, cybersecurity professionals are also actively hunting for vulnerabilities. Even the smallest security gap or brief downtime in internal systems can increase the risk of cyberattacks. Continuous and functional scam detection solutions and exercising threat hunting can strengthen an organization's defense against real attacks.
The role of proxies for phishing prevention
Cybersecurity firms use proxies for various purposes as they strive to combat threat actors.
Unparalleled visibility
To maintain anonymity and better protect their clients, cybersecurity firms often rely on proxies. These proxies are used to conceal their IP addresses, thereby increasing their visibility when monitoring internal systems or conducting web scans for leaked business data. Furthermore, proxies make it harder for malicious actors to detect any activity undertaken by the cybersecurity companies' protection services.
Efficient data gathering
As cybercrimes continue to rise, the demand for precise and up-to-date information has become more pressing. Security experts aim to monitor, gather, and analyze web data that sheds light on the current digital threat landscape. This information is valuable in identifying vulnerabilities, assessing assets, and detecting misconfigurations.
Effective proxies enable efficient data harvesting by overcoming web scraping obstacles, such as anti-bot measures and geographic barriers. Proxies not only provide anonymity but also assist in large-scale data acquisition projects, saving time, resources, and financial funds.
Choosing the right proxies
Since the key to fighting phishing attacks is anonymity, uptime, and speed, datacenter proxies make the perfect choice for cybersecurity.
Datacenter Proxies
Datacenter proxies are a type of proxy server that is not associated with an internet service provider (ISP) or an internet connection at a physical location, such as a home or office. Instead, they are hosted on servers located in data centers, which are large facilities designed to house computing equipment and network infrastructure.
Datacenter proxies offer several benefits, including high speed and reliability, as they are not subject to the same internet connection limitations as residential proxies. They also typically have a large number of IP addresses available, allowing for easier rotation and management of multiple connections.
Datacenter proxies are often used for web scraping, online advertising, and other activities that require high-volume, automated data collection. However, they are also commonly used for malicious purposes, such as launching distributed denial-of-service (DDoS) attacks or conducting large-scale cyber attacks.
As a result, many websites and online services have implemented measures to detect and block datacenter proxy traffic, making it more challenging for legitimate users to access their services using datacenter proxies.
Conclusion
With phishing attacks becoming more sophisticated and highly increasing in numbers, security professionals take a proactive approach and utilize next-level measures to fight against cybercrimes. High-performing proxies provide full visibility of the web, as well as ensure anonymity and smooth data harvesting.